By Michael Still
Your phone isn’t safe.
Believe it or not, there was a time before voice command and GPS tracking when a phone was just a phone. Software plays a major role in making our phones do what they do which impacts in the way we live, work, and play. As a result, our safety and security depend heavily on the accuracy of that software. The slightest problem has the potential to cause catastrophe.

Suraj Kothari, Richardson Professor of Electrical and Computer Engineering at Iowa State University, understands that attacks on a phone’s confidentiality, availability and integrity can be done in ways that elude the security measures that we currently use. Staying safe is not as easy as slapping a password on your phone or logging out of your email account.
“Someone could do something to the software in your phone that gives them access to your GPS location, and from there they can pinpoint your exact location at all times,” Kothari said. “This could become an especially serious problem if someone gained access to a soldier’s phone and interfered with important communication.”
Kothari conducts his research in software engineering, developing appropriate theoretical foundations and building practical tools for improving the productivity and quality of software. He focuses on using smaller mathematical models to dissect and conquer larger, more complex problems.
For an example, he turns to the world of medicine. Like software, our bodies are complex and have complex problems. To better understand this complexity, doctors use Magnetic Resonance Imaging (MRI) scanners.
“Without the MRI, a doctor may suspect a patient has a brain tumor and perform open brain surgery, but that’s very risky. The same principles apply when dealing in software,” said Kothari. “If you have mundane problems, you can get away with what you’re doing, but if you have serious problems, you need something very sophisticated to help solve that problem.”
The MRI scanner is extremely useful in diagnosing serious and complex problems, and without it, medicine would not be as advanced as it is today. In the world of software engineering, Kothari is working on his version of the MRI scanner, devoting research to creating tools to help analyze complex software.
“It’s very difficult for humans to go through millions of lines of code because humans make mistakes. So I had the idea to develop a tool that will transform code,” said Kothari. “We are building software like the Egyptians built the pyramids, using the sheer force of human labor.”
The U.S. Government’s Defense Advanced Research Projects Agency (DARPA) has taken an interest in cyber security, and is concerned with the probability of a digital war in our country’s future. This leaves the Department of Defense searching for the latest and greatest tools in software protection.
“The United States has the most sophisticated fighter jet in the world. With 24 million lines of code, they call it a flying computer,” said Kothari. “Rather than spend the time and money to develop a plane like that, who’s to say enemies won’t focus on trying to sabotage the software in the fighter jet?”
Earlier this year, several nuclear reactors in Iran were attacked by the “Stuxnet” virus. Developed by a joint partnership between the U.S. and Israel, the Stuxnet Virus disabled nearly one-fifth of Iran’s nuclear centrifuges by making them spin out of control. Though Stuxnet represents a very sophisticated, high-end attack, Kothari says this kind of infiltration can happen to anyone, and it doesn’t only affect military software.
“Today, cars have so much software built in – the newest models are even connected to the Internet,” said Kothari. “People have already shown they can get control of a car and make it do what they want it to do. Without proper security, accidents can be caused this way.”
The safety and assurance that software is going to work the way it was designed to work is a critical issue, and the U.S. Department of Defense has developed three focused programs to help aid in the understanding of software.
The first program focuses on controlled systems software, the kind that is used to control complex machines and nuclear reactors. The second program centers on communication infrastructure and handles the way information flows through the Internet and other connected networks. The third program works with smartphone software. This is where Kothari’s research has proven most helpful.
When Raj Aggarwal, Iowa State College of Engineering’s director of Industrial Research Initiatives and managing director of Advanced Research and Technology, told Kothari the Defense Department was looking for software tools to aid in security measures, he was ready to start working.
“This defense project didn’t happen overnight,” said Kothari. “We’ve been doing this for years – even when it wasn’t a hot research area. It takes time to develop software and experiment with it. And we have a background of working with real-world software.”
Funded by a $4.1 million, 3.5-year DARPA grant, the project’s objective is to develop a tool that will detect malware placed unknowingly within applications on the mobile devices.
“The world has been trying to solve security issues by watching what goes through a network, finding suspicious things and then stopping them,” he said. “But now we also need to worry about internal threats and software sabotage. There’s a need to analyze software.”
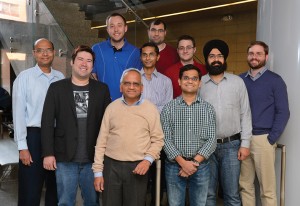
Among the teams awarded smartphone security projects by DARPA, Kothari’s team at Iowa State has earned top rankings based on the speed and accuracy of detecting malware in the challenges posed by the research agency.
“In the end, we’ll have a tool that the Defense Department and other government agencies can use,” Kothari said. “And eventually we’ll be able to make a phone security tool commercially available.”
All of that, he said, will help secure the Defense Department’s smartphones from dangerous attacks and saboteurs.
“We are looking at malicious software that leaves a scattered footprint and that exhibits behaviors that blend with legitimate functionalities of a given application,” he said.
The tool Kothari and his team are designing includes a framework that gathers important information about an app as it scans code for malware. This data is presented in a digestible form that can be analyzed by a person, allowing for more accurate assessments about an app’s intentions than systems currently in place.
“Detecting malware on mobile devices using a completely automated process hasn’t been successful in producing consistent, valuable results,” said Kothari. “We needed a solution that included human interaction, but we also needed to ensure the person analyzing the results could do so without having to parse enormous amounts of information.”
Kothari has partnered with Xuxian Jiang, assistant professor of computer science at North Carolina State University, and Jeremias Sauceda, chief technology officer at EnSoft Corp., on the project.
The team is currently designing, programming, and testing the tool, and is also creating a “cookbook” of properties the tool will use to identify malware-like code. Once implemented, the tool will be flexible enough to be refined and extended to address future malware attacks.
Looking back at his many years of research, Kothari has faced his fair share of challenges and hardships. One of the biggest roadblocks came up early in the process as Kothari was seeking financial assistance with his research.
“Originally, what we were doing was very different from what the funding agencies were interested in, so there were many years where we were not able to get funds. That created a serious problem,” said Kothari. “Funding organizations didn’t start giving much funding to this kind of research until 2011 when the Department of Defense deemed it necessary.”
Despite the challenges he’s encountered, Kothari’s research has resulted in the development of many products and tools that are now being used by more that 250 large companies in 18 countries, including all major auto makers in US, Europe, Japan, and Korea.
“I think one of the biggest rewards is that the work he have done is ultimately being used in the real world. In that way, we are making a difference in everybody’s life,” said Kothari. “Another reward has been working with my colleagues and team of grad and post doc students. Their collaboration has been valuable in our research process.”
Future problems in software security will not easily be solved within the next year or two. According to Kothari, there is still a lot of work that needs to be done. He plans to keep tackling the complexity of software problems, but he can’t do it alone.
“We have to rely on intelligent, motivated, and hard working people to help solve our future problems,” said Kothari. ”Those are the kinds of people we need.”